Secure Web System 927331856 for Businesses
Secure Web System 927331856 offers an end-to-end protective framework with governance, threat modeling, and clear ownership. It emphasizes risk-based prioritization, continuous monitoring, and least-privilege access with persistent encryption. Real-time threat shielding and modular deployments support rapid containment and recovery. The approach ties ROI to governance alignment, balancing speed, cost, and quality for auditable outcomes. Yet questions remain about integration paths, stakeholder responsibilities, and the exact maturity level required to achieve compliant resilience.
What Secure Web System 927331856 Delivers for Businesses
Secure Web System 927331856 delivers a structured, end-to-end framework for protecting business digital assets. It establishes data governance protocols and threat modeling practices that clarify ownership, responsibilities, and risk priorities. The approach enables disciplined decision-making, measurable compliance, and scalable controls. By defining data flows and risk scenarios, it supports freedom through transparent, repeatable security actions and accountable governance.
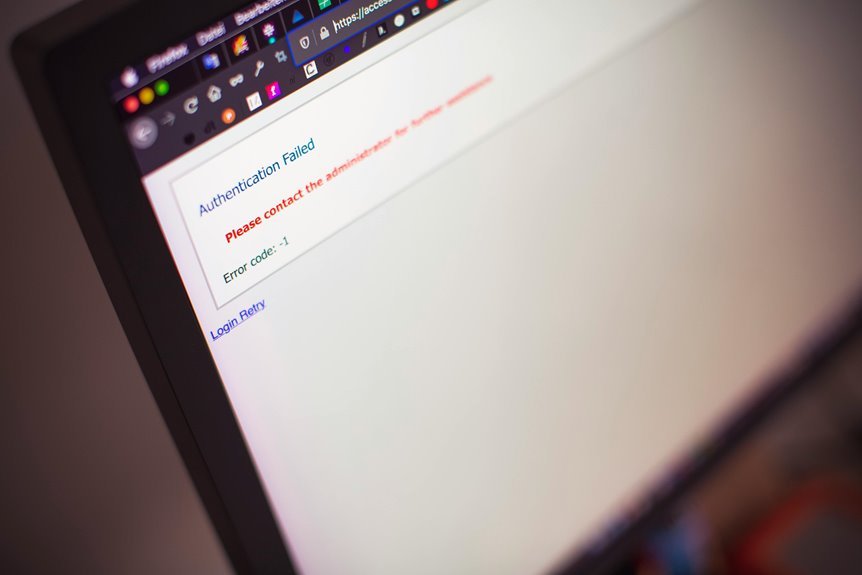
How It Shields Data Across Real-Time Threats
How does a real-time threat landscape shape protective measures across data flows? The system employs layered safeguards that adapt to evolving risks, aligning data protection with continuous monitoring. It leverages threat intelligence to anticipate exploits, apply targeted controls, and minimize exposure. Access is governed by least privilege, encryption remains constant, and incident response is rehearsed for rapid containment and recovery.
Implementing Seamless Deployment and Compliance
Implementing Seamless Deployment and Compliance requires a structured approach that aligns deployment practices with regulatory demands and organizational policies.
The process emphasizes automation, traceability, and modular configurations to minimize risk while preserving agility.
Privacy governance informs data handling and auditing, ensuring transparent stewardship.
Access control enforces least-privilege access, supporting robust separation of duties and continuous compliance monitoring across environments.
Choosing the Right Delivery and ROI Path for Your Team
Choosing the right delivery and ROI path requires a disciplined assessment of capabilities, goals, and constraints to identify the most effective configuration for teams and stakeholders. The approach emphasizes structured evaluation, governance alignment, and measurable outcomes. Data governance informs accountability, while threat modeling clarifies risk boundaries. Strategic selection balances speed, quality, and cost, enabling sustainable outcomes and freedom within disciplined execution.
Conclusion
The Secure Web System 927331856 furnishes a rigorous, auditable framework where governance, threat modeling, and encryption converge to sustain real-time protection. It translates risk into measurable ROI through modular, automated compliance and precise ownership. By orchestrating continuous monitoring and rapid containment, it reduces exposure while maintaining velocity. In short, it delivers disciplined security as a strategic asset, not a cost center—a lighthouse guiding organizations toward resilient, compliant operations and sustainable value. Like a compass, it steadies every decision.